
Network flow data, or NetFlow, is like a treasure trove for network engineers. It's an invaluable source of information about network traffic and yields critical network security insights. This is especially important for identifying indicators of compromise (IoCs), which signal potential security breaches.
In today's cyber threat landscape, where attackers constantly evolve their tactics, techniques, and procedures (TTPs), understanding the movement of data packets is crucial for defending against threats. This article explores why monitoring network flow data is essential for cybersecurity and how it ties into the MITRE ATT&CK framework. We’ll also explore how flow data analysis can enhance:
XDR (Extended Detection and Response),
SIEM (Security Information and Event Management), and
SOAR (Security Orchestration, Automation, and Response) platforms
to efficiently detect and mitigate threats.
In a previous post we discussed the need for a closer working relationship between NetOps and SecOps. The following post explores why network flow data is so critical for protecting enterprise networks.
Understanding Network Flow Data
Network flow data, often referred to as NetFlow (a Cisco protocol) or IPFIX (an IETF standard), captures metadata about communication between devices. This includes:
Source and destination IP Addresses: Who’s talking to whom?
Ports: which applications or services are in use?
Protocols: Are we looking at HTTP, HTTPS, or something else?
Packet and byte counts: How much data is being transferred?
Flow duration: How long is the conversation?
By analyzing this data, network engineers can paint a comprehensive picture of traffic patterns and detect anomalies indicative of malicious activity.
One of the big value-adds that comes from network flow data monitoring is that it can give you application context. Since the COVID era and the explosion of remote work, this context is critical. By monitoring flow data you’ll have insight into the applications your users are using beyond your firewalls. This can be extremely useful in identifying anomalies, such as why is this application being used by this user in this region - possibly flagging a security threat.
Indicators of Compromise (IoCs)
Indicators of compromise are signals that a network or system has been breached. Common IoCs that network flow data can reveal include:
Unusual Traffic Patterns: Unexpected spikes in data transfer or traffic to unusual regions may point to data exfiltration or a command-and-control (C2) connection.
Scenario: Your network typically has consistent data transfer rates during business hours. Suddenly, you notice a significant spike in data transfer during off-hours, such as late at night or on weekends.
Details:
Time: 2 AM - 4 AM
Volume: 500 GB of data transferred to an IP address in a foreign country where your organization has no operations.
Potential Indicator: This may indicate data exfiltration by an insider threat or malware. Unrecognized Protocols or Ports: New services on non-standard ports could suggest lateral movement or tunneling activity.
Scenario: Your network primarily uses common ports like 80 (HTTP), 443 (HTTPS), and 25 (SMTP). Recently, there have been new services communicating over non-standard ports.
Details:
Port: 4444 (typically used by Metasploit for payload handlers)
Protocol: Unknown custom protocol detected
Source: Internal server unexpectedly starts communicating over port 4444
Potential Indicator: This could suggest tunneling activity or lateral movement by an attacker who has compromised an internal server.
Repeated Connection Attempts: High-frequency connections or failed attempts may signal a brute-force attack.
Scenario: You observe a sudden increase in failed login attempts to your VPN gateway.
Details:
Frequency: 1000+ failed login attempts per minute
Source: IP address from a country with no legitimate business operations
Target: Administrator accounts
Potential Indicator: This high-frequency of failed login attempts might signal a brute-force attack aiming to gain unauthorized access.
Increased Internal Traffic: Once inside, attackers may scan or move laterally within the network, increasing internal traffic to unusual levels.
Scenario: Your internal network traffic suddenly increases, especially in segments that typically see minimal activity.
Details:
Affected Segment: Internal subnet dedicated to HR department
Traffic Increase: 200% rise in internal traffic between HR workstations and the main file server
Time: During normal working hours, but with unusual patterns such as consistent intervals of high activity.
Potential Indicator: This could indicate an internal scan or lateral movement, where an attacker is trying to identify other vulnerable systems or access sensitive files.
The Relevance of the MITRE ATT&CK Framework
The MITRE ATT&CK framework is a curated knowledge base of adversarial tactics and techniques derived from real-world observations. It categorizes tactics like initial access, persistence, and data exfiltration into specific techniques and sub-techniques. It provides a detailed map of how attackers operate enabling the good guys to gain situational awareness, quickly.
Using the last IOC example of an incident of increased internal traffic, here is the information that ATT&CK could provide:
1. Tactic: Discovery
Technique: Network Service Scanning (T1046)
Description: The attacker may be scanning the internal network to discover services running on other machines, identify open ports, and gather information about the network's layout.
Indicators: Increase in internal traffic due to scanning activities.
Technique: System Network Connections Discovery (T1049)
Description: The attacker might be examining the network connections on the compromised HR workstations to map out potential targets for lateral movement.
Indicators: Consistent intervals of high activity as the attacker gathers data.
2. Tactic: Lateral Movement
Technique: Remote Services (T1021)
Description: The attacker may use remote services to move laterally within the network, exploiting legitimate services to access other systems.
Indicators: Traffic between HR workstations and the main file server, especially if it involves remote desktop protocol (RDP), SSH, or SMB traffic.
Technique: Internal Spearphishing (T1534)
Description: The attacker may attempt to gain credentials from HR personnel to facilitate lateral movement.
Indicators: Increased email traffic with suspicious attachments or links within the HR department.
3. Tactic: Collection
Technique: Data from Local System (T1005)
Description: The attacker might be collecting sensitive files from the HR workstations to exfiltrate.
Indicators: Unusual file access patterns, especially to sensitive documents.
Technique: Automated Collection (T1119)
Description: The attacker could be using scripts or malware to automatically gather files from the compromised systems.
Indicators: High volume of internal traffic due to automated data collection processes.
4. Tactic: Exfiltration
Technique: Exfiltration Over Web Service (T1567.002)
Description: The attacker may use web services to exfiltrate collected data.
Indicators: Outbound traffic to external IPs or domains not commonly accessed by the HR department.
Network flow data, when mapped to the MITRE ATT&CK framework, provides a structured and comprehensive approach for understanding and classifying potential attacks.
Enhancing XDR, SIEM, and SOAR Platforms
Monitoring network flow data can significantly enhance the detection and response capabilities of XDR, SIEM, and SOAR platforms.
1. Extended Detection and Response (XDR)
XDR integrates data from various security tools, providing a unified threat detection and response solution. Network flow data is essential here because:
Comprehensive Threat Context: Flow data adds network-layer visibility to endpoint detection, providing comprehensive insights into attack campaigns.
Correlating Suspicious Events: Anomalies detected in flow data can be cross-referenced with endpoint or application data for a fuller picture.
Proactive Threat Hunting: Historical flow data helps identify attack patterns and facilitates proactive threat hunting.
2. Security Information and Event Management (SIEM)
SIEM platforms collect and analyze security data to identify potential threats. Network flow data’s contribution includes:
Real-Time Anomaly Detection: Flow data helps recognize deviations from established baselines.
Correlating Network and System Logs: Correlating flow anomalies with system and application logs can highlight compromised systems.
Forensic Investigation: Flow data provides a detailed historical record useful in post-breach investigations.
3. Security Orchestration, Automation, and Response (SOAR)
SOAR platforms automate threat response processes and orchestrate remediation activities. Here’s how network flow data fits in:
Automated Playbooks: Automatically trigger remediation playbooks when specific flow anomalies are detected.
Cross-Platform Coordination: Coordinate responses across multiple security tools by combining flow-based detections with other sources.
Reduced False Positives: Correlating flow data with alerts from other sources reduces false positives, improving response accuracy.
Implementing Effective Network Flow Monitoring
To leverage network flow data effectively for threat detection, consider these best practices:
Baseline Normal Behavior: Understand normal traffic patterns to distinguish benign from malicious activity.
Deploy Flow Exporters Widely: Collect data from network switches, routers, and firewalls to cover the entire network.
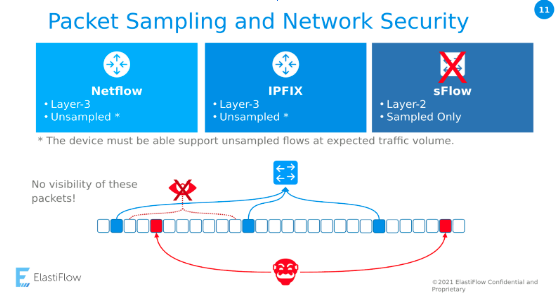
Collect Unsampled Flow Records: Many Network Observability solutions only sample flow data in an attempt to save storage and processing costs. This can be especially dangerous when it comes to identifying covert threats. Subtle explorations or infiltrations may be missed by sampling.
Use Threat Intelligence Feeds: Cross-reference flow data with threat intelligence to identify known malicious IPs and domains.
Integrate with Existing Platforms: Feed flow data into XDR, SIEM, and SOAR platforms for automated and coordinated threat detection and response.
Analyze Anomalies: Prioritize investigating anomalies based on their risk impact and relevance to your specific network architecture.
Conclusion
Monitoring network flow data is crucial for network engineers seeking to identify indicators of compromise early. In combination with frameworks like MITRE ATT&CK, it provides an unparalleled view into attacker TTPs, allowing defenders to understand and anticipate malicious activity. When integrated into XDR, SIEM, and SOAR platforms, flow data becomes a powerful tool for rapidly detecting and mitigating threats efficiently and effectively.
Having comprehensive tools in place to monitor your NetFlow activity helps move you from Detection and Prevention to Network Detection and Response. Network Flow data has three great properties that you just don't find in other data sources for cyber security:
It’s grounded in fact - if you see it on the network you know that it happened
It can’t be adulterated or tampered with, and
You can’t turn it off without anyone noticing.
Network engineers should prioritize comprehensive network flow monitoring to stay ahead in the ever-evolving cybersecurity game.
Update June 2024: Since publishing this post, ElastiFlow has launched NetIntel, a product that enhances and enriches flow data with significantly more threat intelligence information.
Stay connected
Sign up to stay connected and receive the latest content and updates from us!